
A vulnerability on internet and cable TV provider Spectrum's website made it possible for just about anyone to take over customers’ accounts without a password. Only a Spectrum customer’s IP address (a number unique to every Internet-connected device) was required to exploit the flaw, which security researchers Phobia and Nicholas “Convict” Ceraolo discovered.
After BuzzFeed News shared the previously unreported findings with parent company Charter Communications, spokesperson Francois Claude said, “We investigated and quickly implemented a fix to the vulnerability that was brought to our attention. We continue to investigate, but at this time have no reason to believe this vulnerability was ever used beyond the security researchers who reported it to BuzzFeed.”
With access to a customer’s internet and cable TV provider account, a hacker can see sensitive personal data like their billing address, email, and account number. That information could be used to social engineer — in other words, deceive — customer support personnel, who could be fooled into giving up more of a target’s data, or even to trick the customer with phishing emails that look like they are legitimate because they include accurate, detailed personal info related to their internet account.
The myTWC app, which an account provides access to, also shows the MAC address (a number that identifies each device on a network) of any equipment connected to the service. This can be used to impersonate another computer or router on a Wi-Fi network, and perform a man-in-the-middle type of attack to capture all of that network’s web traffic and acquire any data submitted to non-HTTPS sites, including login credentials.
If you have information or tips, you can contact this reporter over the encrypted chat service Signal at 415-943-0446. You can also send an encrypted email to nicole.nguyen@buzzfeed.com, using the PGP key found here.
Charter Communications, the second largest cable provider in the US, provides residential Internet access to 23 million customers. In 2016, Charter purchased Time Warner Cable and Bright House Networks, and merged the two internet companies under the Spectrum brand.
Claude noted that only a subset of Time Warner Cable’s 14 million pre-merger “legacy” customers — those without a “TWC ID” (an account through which they can pay for bills and watch TV online) — were affected by the security flaw. The spokesperson did not reveal exactly how many people are in that group, and only stated that the number is “significantly less” than the company’s subscriber base.
Spectrum does not require its customers to register for a TWC ID, but according to the Charter spokesperson, the “majority” of its legacy customers have already registered.
A registration page where subscribers can create a TWC ID contained the crucial security flaw. If the targeted customer had not registered for a TWC ID, a hacker could trick the website and gain full access to the target’s account by replacing their own IP address with the customer’s using the “X-forwarded-for” technique, which can be executed even by technically unsophisticated hackers with a simple browser extension.
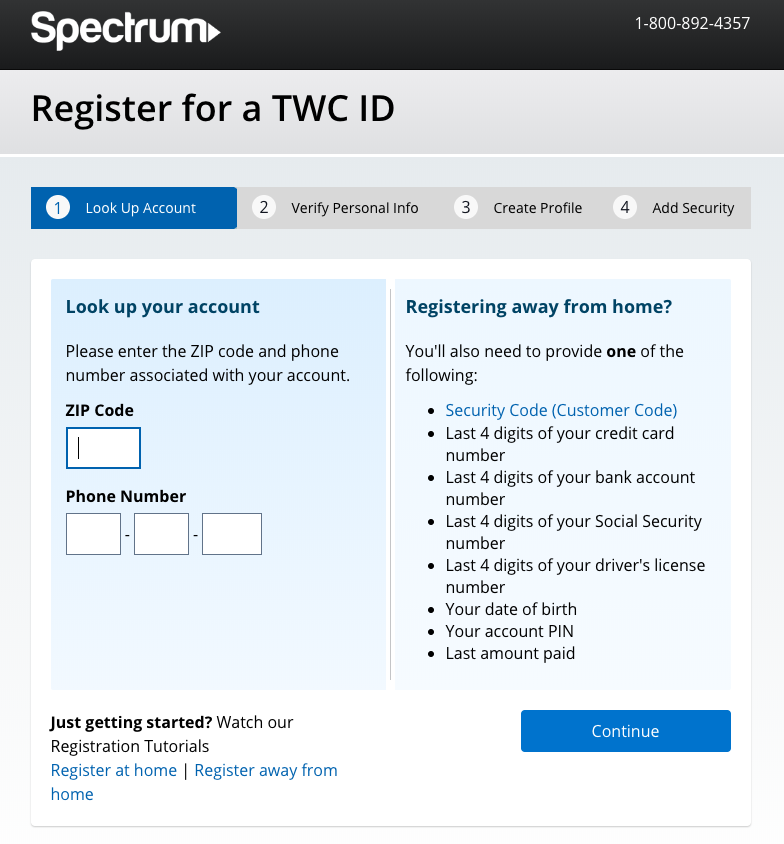
The registration website tried to verify subscribers’ identities by asking for their zip codes and phone numbers. But according to the security researcher Phobia, the zip code didn’t need to be correct to proceed to the next page. Only the phone number associated with the account needed to be accurate. Additionally, Ceraolo found that hackers could use a brute-force software program in the phone number field (in other words, repeatedly try different 10-digit combinations), because the Spectrum website did not limit the number of attempts. That means it would be relatively easy for a hacker to take over someone’s account even without an accurate phone number.
With the spoofed IP address and correct phone number, hackers could register for a new TWC ID on an existing Time Warner Cable subscription, and obtain complete access to the customer’s account.
If a customer tries registering for a TWC ID from a different IP address than their home location’s, Spectrum does require another form of identification (like their bank account number, driver’s license, or the last four digits of an account holder’s Social Security number), in addition to the zip code and phone number. However, this did not protect against hackers spoofing the customer’s IP.
According to Marc Laliberte, senior security analyst at WatchGuard Technologies, IP address verification makes logging in simple for less tech-savvy users, but it sacrifices security for usability: “While I don’t know the specifics of this case, generally [IP address verification] makes it easier for someone like my mom to hop on to her account online, but falls victim to the same vulnerability as a single password, instead of multi-factor authentication.” Having that password — or IP address — is like having the “keys to the kingdom,” Laliberte said.
IP addresses are readily available to anyone who’s looking for them — and bad actors can easily use them to target and harass someone. Web administrators can see the IP addresses of every site visitor, and many online forums display users’ IP addresses in their profiles. And once someone has a target’s IP address, they can use IP lookup tools to find that person’s internet service provider, as well as their location.
Spectrum isn’t the only company with IP address verification vulnerabilities. Comcast exposed its customers’ partial address through a security vulnerability in a similar in-home authentication method, and the company recently disabled the page after a BuzzFeed News report.
Time Warner has left its customers’ data vulnerable before. In 2017, software developer Kromtech revealed that millions of Time Warner customers’ records, including usernames and financial transactions, were available on servers without password protection. Neither Time Warner nor its new parent company, Spectrum, offers a submission form or payment for security researchers who want to report discovered vulnerabilities. Many other companies, like Google and Microsoft, pay researchers a bounty for submitting security flaws.
