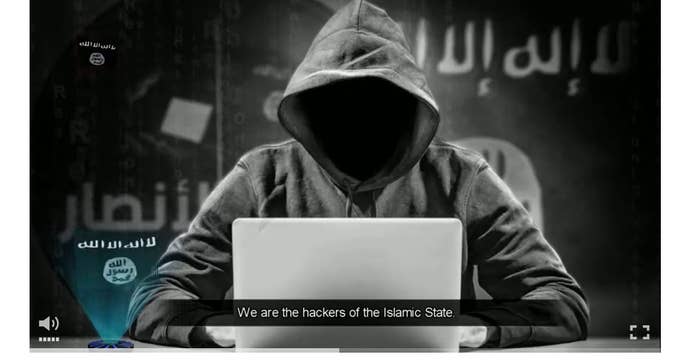
Hackers claiming to be affiliated with ISIS threatened a series of cyberattacks against the U.S., Europe, and Australia Monday, in the first video to be released by a group calling itself the "Islamic State's Defenders in the Internet."
"Praise to Allah, today we extend on the land and in the internet. We send this message to America and Europe. We are the hackers of the Islamic State and the electronic war has not yet begun," says an altered voice in a video reminiscent of the Anonymous hacker group. "What you have seen is just a preface of the future. We are able until this moment to hack the website of the American leadership and the website of the Australian airport and many other websites."
Cyber experts who focus on ISIS, however, have expressed doubt about the hacking-prowess group — more widely known as the Cyber Caliphate — and see the most recent video as an attempt to capitalize on the media attention recently paid to Junaid Husain, a U.K.-born hacker who is currently thought to be in Syria and who appears to have exchanged tweets with one of the gunmen in the attack on Garland, Texas, last week.
Tweets by Husain, who goes by "TriCk" online, have provided the only direct link between ISIS and that attack. British authorities now say that Husain is a dangerous hacker who has previously managed to crack bank security systems, as well as taking part in attacks against involving former Alaska Gov. Sarah Palin, NASA, NATO, the United Nations, BlackBerry, and the English Defense League alongside his former collective, TeaMp0isoN.
Following previous attacks, Anonymous — the collective of hackers, trolls, and teen hangers-on — has declared that it would launch counterattacks on known ISIS accounts. So far on Monday, accounts on Twitter did not seem impressed by the new threats by the Cyber Caliphate as put forward in its video.
#ISIS #CyberCaliphate using #HelloftheAmericansystem to spread their nonsense. I'm scared. ;)
Was the #ISIS attack supposed to be 2pm Eastern Time or 2pm Medieval TIme? @DeptofDefense #HelloftheAmericansystem
What do you get when the media anoints Junaid Hussein as a celebrity? Low theater of the absurd.
The style of the video released Monday was a departure from previous videos released by ISIS-linked accounts, said J.M. Berger, co-author of the book ISIS: The State of Terror and a fellow at the Brookings Institute.
"It suggests this may have been thrown together pretty quickly to exploit the publicity from Garland. However the differences may also be intended to present more of a hacker façade," said Berger.
Since January, a group of hackers going by the name "Cyber Caliphate" have claimed responsibility for several attacks, the most widely publicized of which was the hacking of U.S. Central Military Command's @CENTCOM Twitter handle and YouTube page. In a message later posted to Pastebin, the group also claimed to release confidential U.S. Army files, thought it appeared that many of those files were available online and were not confidential. The same channels that distributed the claims of that attack pushed Monday's new video.
"In principle, it is certainly quite possible they have cyber capabilities that they haven't displayed publicly yet, but until we see evidence of such, it's hard to put a level on the threat," said Berger. "People are concerned, but the damage done so far has been minimal."
"The d0xing activities were the most significant," he added, using the term for revealing private details of accounts broadly online, "but it's not clear they deployed any hacking muscle to get that information, and they may have accessed data from previous hacks by other parties or used other open-source tools."
