
Comcast Xfinity inadvertently exposed the partial home addresses and Social Security numbers of more than 26.5 million customers, according to security researcher Ryan Stevenson, who discovered the security flaws. Two previously unreported vulnerabilities in the high-speed internet service provider’s online customer portal made it easy for even an unsophisticated hacker to access this sensitive information.
After BuzzFeed News reported the findings to Comcast, the company patched the flaws. Spokesperson David McGuire told BuzzFeed News, “We quickly investigated these issues and within hours we blocked both vulnerabilities, eliminating the ability to conduct the actions described by these researchers. We take our customers’ security very seriously, and we have no reason to believe these vulnerabilities were ever used against Comcast customers outside of the research described in this report.”
While Comcast has not found any foul play yet, its review is ongoing.
If you have information or tips, you can contact this reporter over the encrypted chat service Signal at 415-943-0446. You can also send an encrypted email to nicole.nguyen@buzzfeed.com, using the PGP key found here.
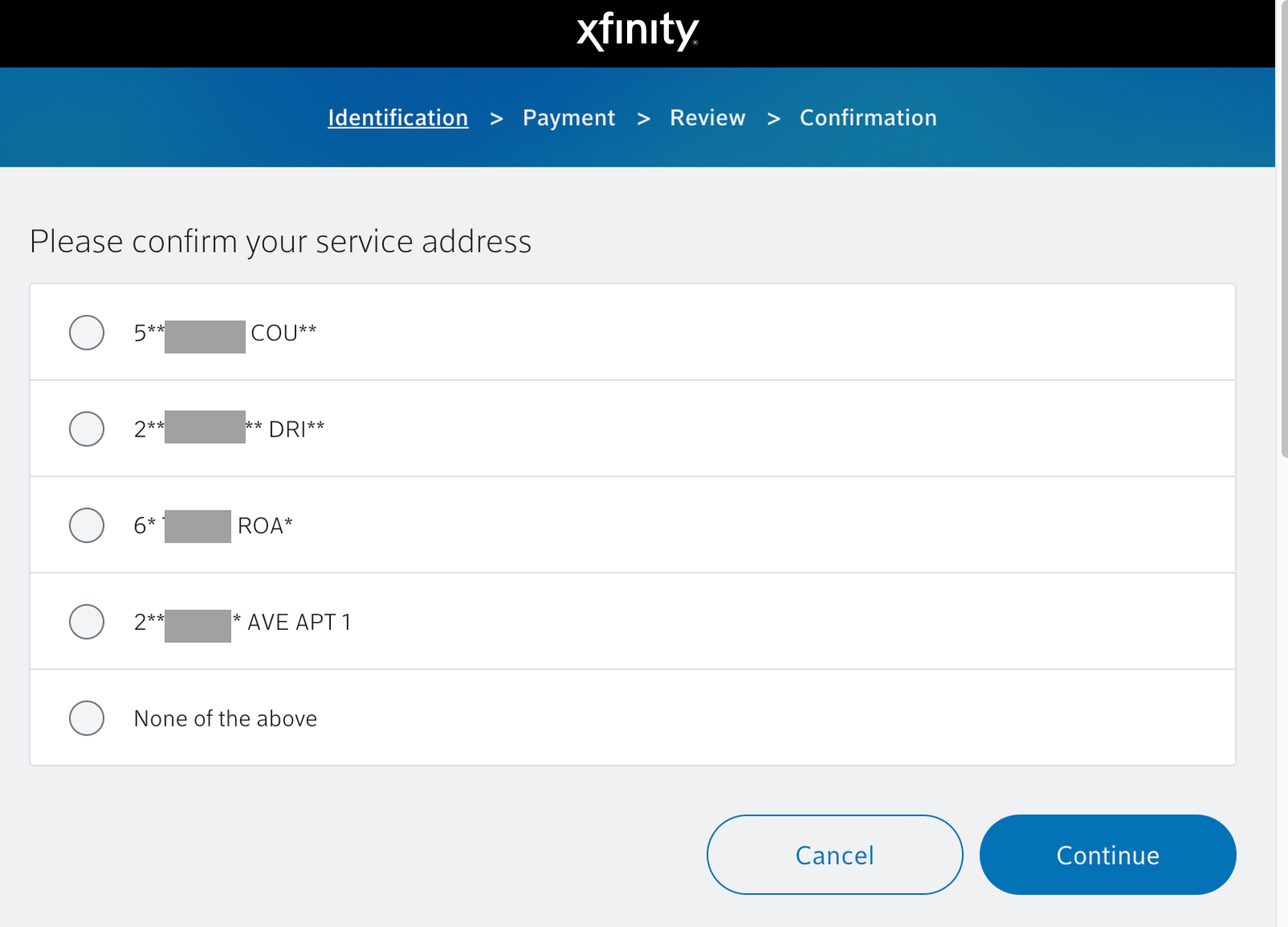
One of the flaws could be exploited by going to an “in-home authentication” page where customers can pay their bills without signing in. The portal asked customers to verify their account by choosing from one of four partial home addresses it suggested, if the device was (or seemed like it was) connected to the customer’s home network. If a hacker obtained a customer’s IP address and spoofed Comcast using an "X-forwarded-for" technique, they could repeatedly refresh this login page to reveal the customer’s location. That’s because each time the page refreshed, three addresses would change, while one address, the correct address, remained the same.
Eventually, the page would show the first digit of the street number and first three letters of the correct street name, while asterisks hid the remaining characters. A hacker could then use IP lookup websites to determine the city, state, and postal code of the partial address.
After learning of the vulnerability, Comcast disabled in-home authentication. Now, customers need to manually input personal information to verify their accounts.
This vulnerability was particularly easy to exploit — and use to target someone. It’s simple to obtain someone’s IP address (or “Internet Protocol”), a string of numbers that links your internet activity to the Wi-Fi network you’re using. Web administrators can see the IP addresses of everyone who visits their website. Many forums also disclose users’ IP addresses, along with their usernames. A malicious actor can also send someone a link designed specifically to obtain a target’s IP address.
While an IP address alone is not sensitive information, paired with the knowledge of someone’s internet service provider, it can help a bad actor confirm their target’s specific location. And often, it’s fairly easy to figure out someone’s internet service provider, or ISP, because an area is typically limited to one or two high-speed internet options, thanks to the consolidation of internet companies.
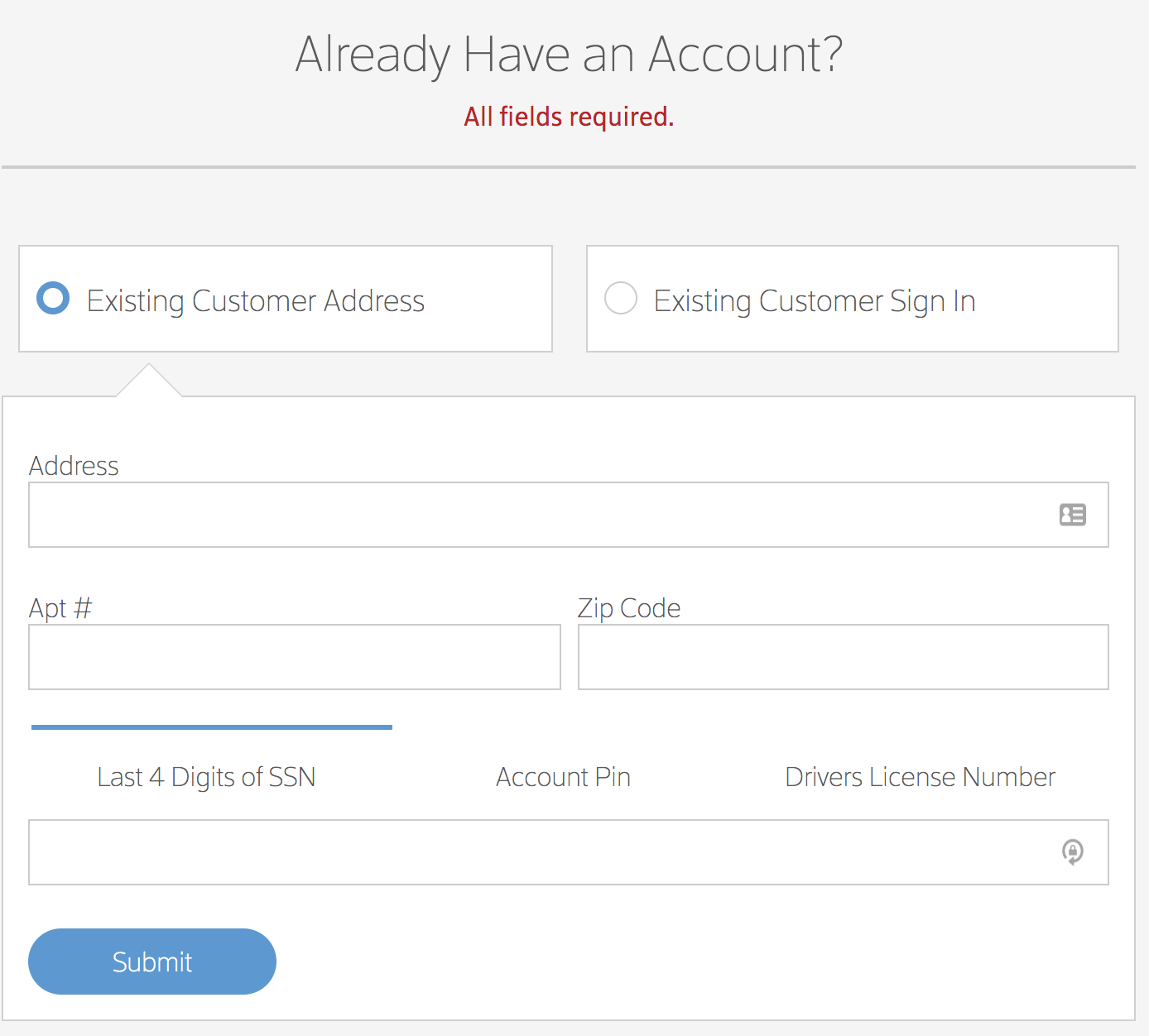
In the second vulnerability that Stevenson discovered, a sign-up page through the website for Comcast’s Authorized Dealers (sales agents stationed at non-Comcast retail locations) revealed the last four digits of customers’ Social Security numbers. Armed with just a customer’s billing address, a hacker could brute-force (in other words, repeatedly try random four-digit combinations until the correct combination is guessed) the last four digits of a customer’s Social Security number. Because the login page did not limit the number of attempts, hackers could use a program that runs until the correct Social Security number is inputted into the form.
After being contacted by BuzzFeed News, Comcast put a strict rate limit on the portal.
Social Security information is particularly sensitive because many companies, including credit card companies and wireless service providers, use the last four digits of your Social Security number to verify your identity over the phone or online. Hackers can use this four-digit combination to steal your identity by tricking customer service representatives into handing over online account access.
“An attacker having partial address information and combining it with partial Social Security numbers information is a recipe for disaster,” said Jessy Irwin, head of security at Tendermint. The last four digits of a Social, according to Irwin, can get an attacker into nearly every type of account.
“We really need to move away from using those kinds of information,” said Irwin, who said even partial Social Security and address information is too risky and too easy to find in a web search or account settings.
Security researchers like Stevenson who find vulnerabilities in Comcast products and services can report them through a submission form. However, the company’s disclosure policy states that it “does not offer a bounty program or provide compensation in exchange for security vulnerability submissions,” unlike other reporting programs that companies like Github, Google, and Microsoft offer. (Stevenson did not submit his findings to Comcast.)
While internet service providers like Comcast aren’t necessarily less secure than other websites, “they’re just more risky because of the data they hold,” said Irwin. That data includes ties to a cellphone account, which can be used to hijack a SIM card and bypass two-step verification.
The disclosure of these vulnerabilities follows a slew of massive breaches over the past year, including credit monitoring firm Equifax, Yahoo, the UK’s National Health Service, and, most recently, Reddit. These hacks show the increasing eagerness (and ability) of hackers to access sensitive data, and the importance of implementing security measures that keep users’ personal information safe. It’s also worth noting that when companies like Equifax and Yahoo recently reported their massive data breaches, both later found the leaks affected more users and data than initially announced.
