"We have just released a very important security update for our iPhone and iPad apps addressing an issue that allowed passwords to be compromised in certain circumstances," Tumblr told its users on its staff blog. "Please download the update now."
It was an unusually terse note with an alarming follow-up: "If you've been using these apps, you should also update your password on Tumblr and anywhere else you may have been using the same password." If you've been using these apps? What iOS user with a Tumblr account doesn't use these apps? Tumblr — or Yahoo, really — is asking tens of millions of people to change their passwords without really explaining why.
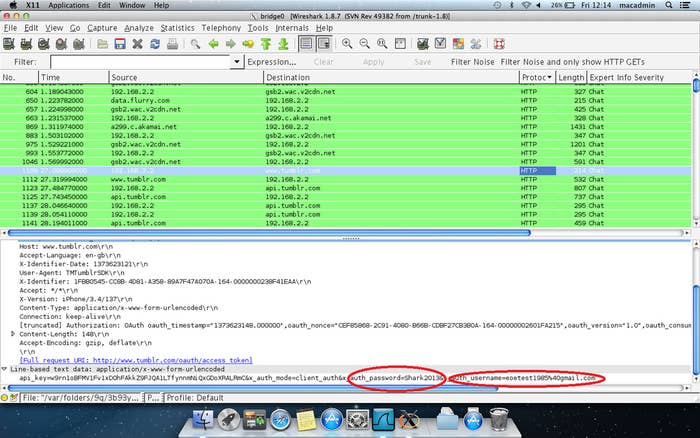
So, how bad was the flaw? Awfully bad. Tumblr's iOS apps evidently didn't encrypt user passwords before sending them to Tumblr's servers, meaning that if you logged in to your Tumblr iPhone app on public Wi-Fi, anyone with the desire to steal your information could easily do so with a free program like Firesheep. Security researcher Graham Cluley explains:
If an app like Tumblr doesn't login through a secure (SSL) server, anybody on the Wi-Fi network you are using could grab your username and password, as they are transmitted from your app to Tumblr.
That's because, without HTTPS, they are sent as unencrypted text.
This is not a breach, which is usually why companies ask their users to reset passwords, but a flaw. As such, this probably does not mean that your password has been stolen. What it does mean is that, since there has been a Tumblr iPhone app, it has been possible for someone in the same room as you to target you for password theft. Even if this sounds unlikely, there's no easy way to find out if this has happened to you, which is why Tumblr had to ask so many people to take immediate action.
Most major login-based iPhone apps use SSL by default, including Gmail and Twitter, for specifically this reason: It protects users from a very simple form of attack. The real question is why it took Tumblr so long to do the same.
In any case, you should follow Tumblr's advice, just in case.
The Register, which first reported on the flaw before Tumblr had acknowledged it, shows just how easy it was to exploit: