A group of hackers based in China has leveraged the coronavirus crisis to attack the public and telecom sectors in Mongolia by impersonating the country’s foreign ministry, according to cybersecurity firm Check Point.
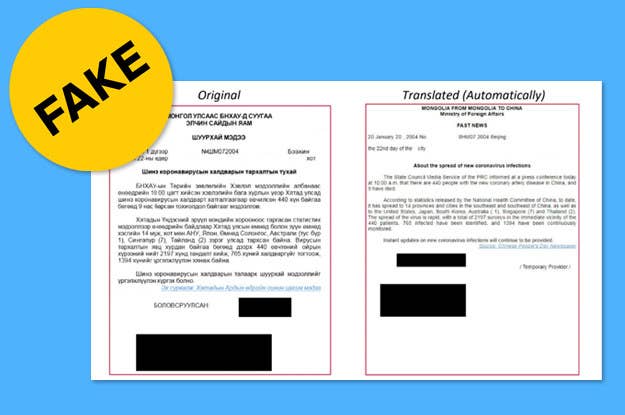
The attack, which researchers at Check Point dubbed "Panda-19," faked two documents from the Mongolian minister of foreign affairs. The documents were disguised as updates on the prevalence of the coronavirus cases in Mongolia, but opening them would infect the target’s computer with a tool called RoyalRoad, which would take over the devices without users' knowledge.
The hackers, who have not been identified, have been in operation since 2016 — and the outbreak of the virus has not slowed them down.
“It seems like the situation in China hasn't been affecting this group,” Lotem Finkelstein, Check Point's head of threat intelligence, told BuzzFeed News.
“It is still unclear why they were targeting these specific organizations,” Finkelstein said. “But we know that they were trying to steal documents and to remote control these systems.”
Once the attachment in the email was opened and downloaded, malware would control the infected computer, allowing the attackers to take screenshots and steal information. According to Finkelstein, gaining remote access is a “very advanced capability.”
As a result of the Panda-19 attack, Finkelstein said they were able to fingerprint the group, meaning they can now track it further and help thwart future attacks. The Chinese hackers, previously known for their operations in the Eastern Hemisphere, frequently go after high-profile targets like Russian telecom companies and targets in Ukraine and Belarus.
The coronavirus hacking attacks are going to get worse before they get better, Finkelstein said. “We have seen them active for four years with no intention to stop,” he said. “So we believe that they will use the coronavirus situation [because] it is very effective.”
Check Point has also been tracking malicious domain registrations using COVID-19 keywords. Another firm, Reason Cybersecurity, has tracked fake coronavirus tracking websites set up by hackers attempting to infect users with malware. The data is genuine, Hacker News reported — but if users were to download the app, their passwords would be stolen.
Other researchers have also pointed to a high amount of phishing emails using the coronavirus as lures. These attackers have impersonated the CDC, the World Health Organization, and executives or members of HR departments.
“Coronavirus has been exhausting for us,” Sherrod DeGrippo, senior director of the threat research and detection team at Proofpoint, previously told BuzzFeed News.
CORRECTION
Lotem Finkelstein's name was misspelled in an earlier version of this post.
