
The gay dating app Grindr is still exposing the precise location of its more than 3.6 million active users although it has long been aware of the issue. According to experts, there is a simple tweak that would protect users, but Grindr hasn’t implemented it.
In a post published Thursday, the website Queer Europe detailed how easy it is to find any Grindr user’s location using an app called Fuckr, which employs a technique called “trilateration” to find users. Fuckr, which can be downloaded for free and is not affiliated with Grindr, is built on top of unauthorized access to Grindr’s private API, or “application programming interface,” which provides Fuckr with information in Grindr's database.
Grindr is not deliberately revealing the locations of its users. But the “incredibl[y] high level of precision” of the distance data Grindr collects and shares allows apps like Fuckr to pinpoint users’ whereabouts, according to security researcher Patrick Wardle.
The highly precise distance data Grindr collects and shares allows apps like Fuckr to pinpoint users’ whereabouts.
GitHub, which has hosted the Fuckr repository since it was released in 2015, disabled public access to the app shortly after the Queer Europe post published, citing Fuckr’s unauthorized access to the Grindr API. However, dozens of “forks” (modified versions) of the app are still available on GitHub. Queer Europe also confirmed to BuzzFeed News that the Fuckr application remains operational and can still make requests for up to 600 Grindr users’ locations at a time. Neither Grindr nor Github responded to request for comment about Fuckr’s takedown.
In a statement to BuzzFeed News, Grindr president Scott Chen argued that the app’s geolocation feature is “core to our platform and user experience,” but also acknowledged that “there are inherent challenges in the use of any app that utilizes or relies upon location information.” Chen added, “Additionally, we currently utilize a geohash system, which approximates, rather than ‘pinpoints,’ all location information.” He also said that Grindr “will continue trying to evolve and improve our platform,” but did not specify how.
However, according to Queer Europe, applications like Fuckr don’t simply use Grindr’s location data to “approximate” users’ locations. They reveal their exact location, alongside photos and other information available on Grindr profiles, including body type, ethnicity, HIV status, last HIV test, and sexual position preference.
Additionally, while the app does hide location by default for users in some countries where LGBT people are persecuted, Queer Europe found that location is still enabled by default in other places where the LGBT community faces discrimination: Algeria, Turkey, Belarus, Ethiopia, Qatar, Abu Dhabi, Oman, Azerbaijan, China, Malaysia, and Indonesia.
Grindr did not respond to BuzzFeed News’ inquiry regarding why Fuckr, an unauthorized third-party, is able to access Grindr’s private API. Because users input their legitimate Grindr username and password in order to access the Fuckr app, it’s unclear whether it’s possible for Grindr to close the loophole that gives Fuckr access to its data.
It’s not the first time Grindr has exposed sensitive information. In April, BuzzFeed News reported that the app was letting other companies see users’ HIV status. After first defending its decision, Grindr eventually stopped sharing the information with third-party analytics firms.
“I was shocked by the accuracy with which I could follow and track his movements."
Using Fuckr, the Queer Europe post’s author, S.P., who asked to remain anonymous, was able to track a friend on Saturday night (with his consent) as he traveled to a restaurant, then a sauna, then an address that wasn’t his home. “I was shocked by the accuracy with which I could follow and track his movements,” S.P. told BuzzFeed News.
S.P. then used the app to monitor his own whereabouts. The app’s location tracking was precise: It pointed to the exact corner in his garden where he was sitting.
Applications designed to locate Grindr users are publicly available online, and give anyone access to a virtual map on which you can travel from city to city, and from country to country, while seeing the exact location of cruising men that share their distance online. https://t.co/0IumD6laAE
“Users of location-based dating apps often assume that they only share their information with other men nearby them,” S.P. said. But the reality, he noted, is that anyone — even those who don’t know how to code — can obtain Grindr users’ locations without their knowledge.
Many Grindr users are concerned that the app exposes their locations. One Grindr user named Osahon Osa, who lives in Ohio, told BuzzFeed News, “Although it is your decision to send your location to a random stranger for a hookup or meet up, the fact that anybody can do it with a click of a button? That’s alarming.” Javonti Thomas, a former Grindr user, said, “Third-party sites having access to where you are and who you are is detrimental.”
In a Twitter poll with over 460 respondents that addressed Grindr users, 60% said apps that are able to pinpoint their location are “scary,” while 24% didn’t know that was possible. Sixteen percent said that it’s a feature, not a bug. (BuzzFeed News could not verify if all respondents were actual Grindr users.)
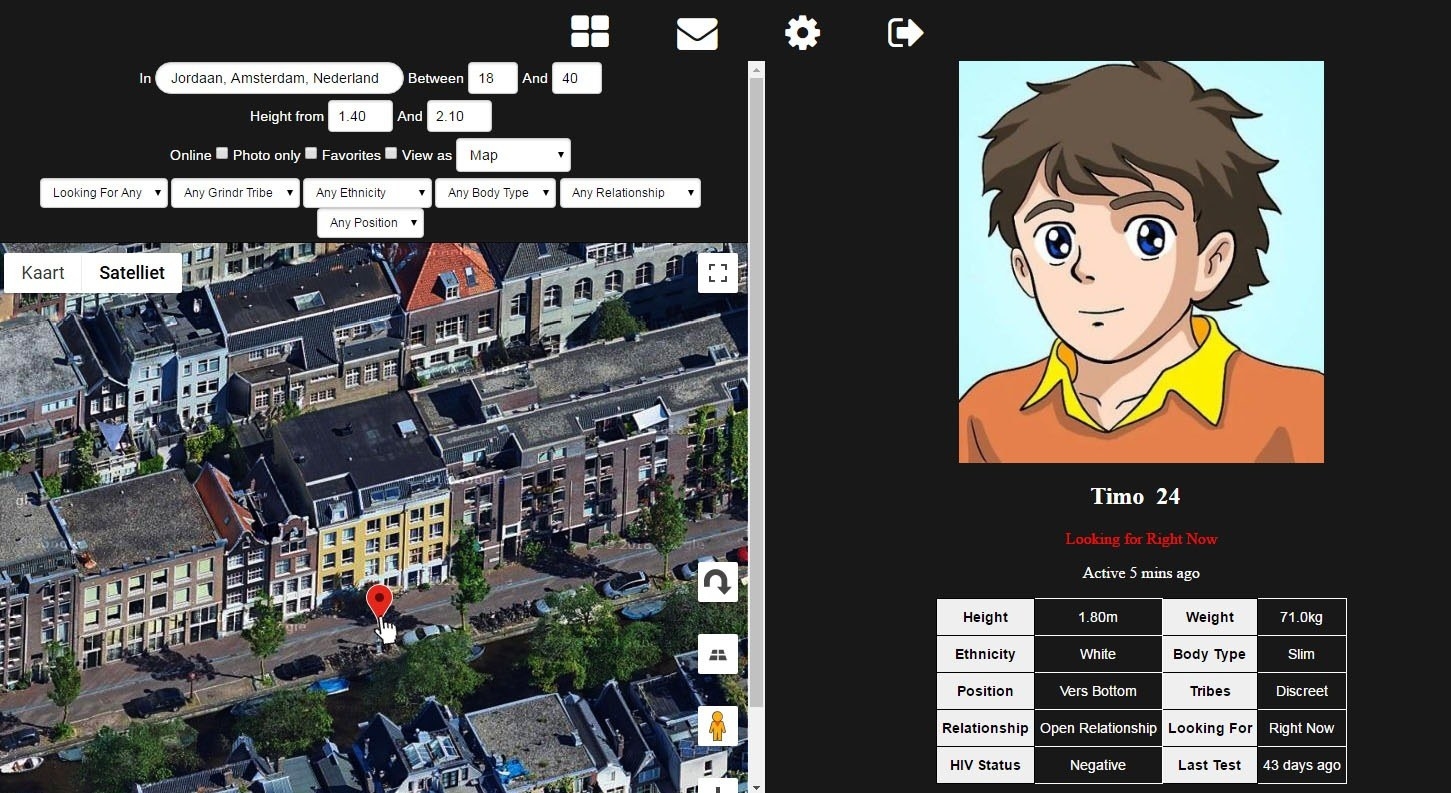
Fuckr has a simple interface: Users can move around a map with marker icons that indicate the location of Grindr users and filter the results by height, ethnicity, body type, or sexual position preference. Clicking on a marker reveals the user’s profile. Fuckr updates the user’s location when they open their Grindr app. While it’s not possible to search for an individual user by name, it is possible to use the aforementioned filters, plus the app’s city/address field, to narrow results. And users are able to view the location of profiles they have messaged with by navigating to Fuckr’s chat section and clicking on the globe icon next to those users' profiles.
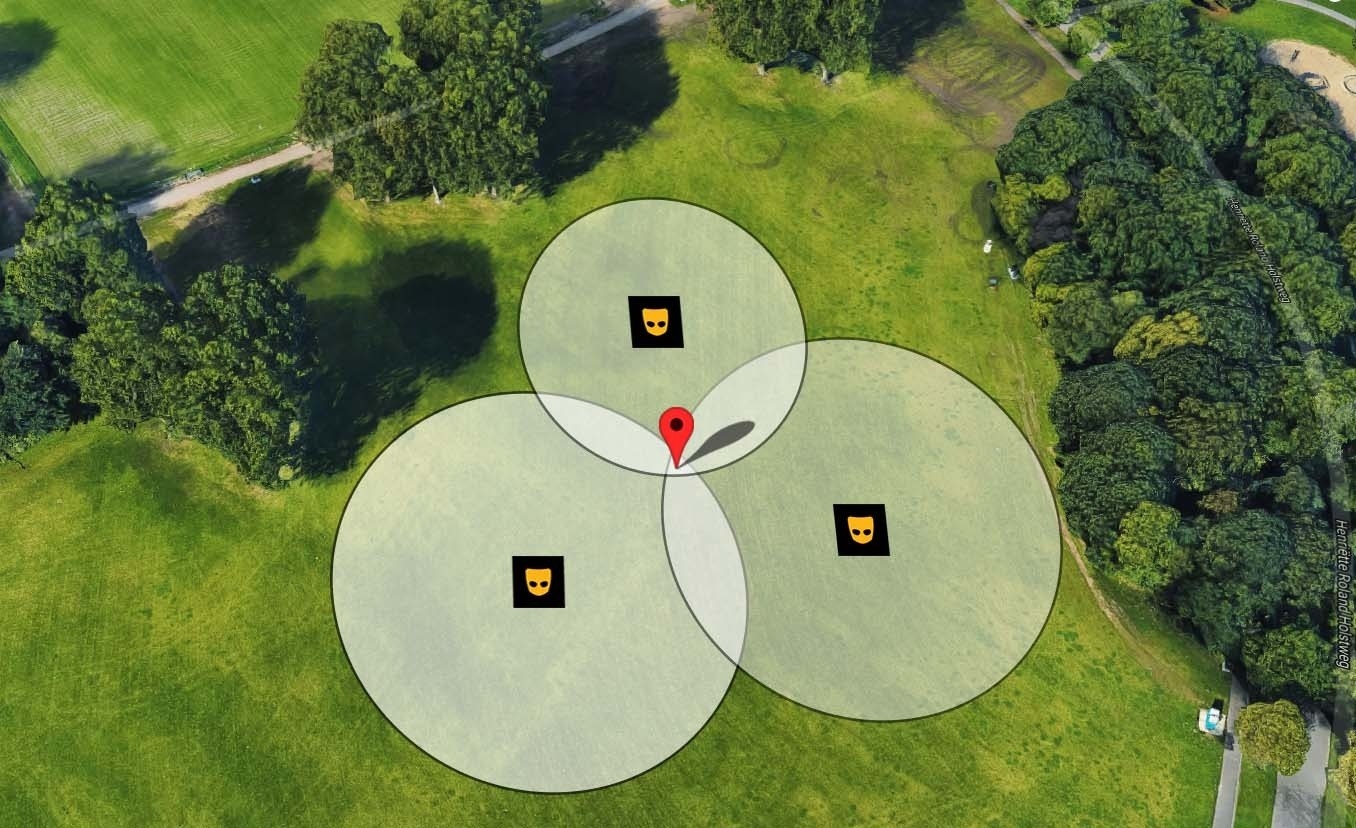
Fuckr works by taking Grindr users' location data (which appears in the app as “X feet away”) and moves a virtual Grindr account closer to and farther away from a target. Using three additional distances as data points, the app can then triangulate where the target is.
Grindr has long been aware that its app allows third parties to track its users everywhere they go. In 2014, Wardle, the security researcher, discovered how to reverse-engineer Grindr data through trilateration, and shared the issues with Grindr. In 2016, security researcher Nguyen Phong Hoang found that Grindr’s ordering of nearby users by proximity can reveal the location of those users (even those who disable distance info) through what’s called a “colluding” trilateration attack. And in March 2018, security researcher Trever Faden raised concerns about Fuckr.
There are straightforward solutions Grindr could employ to protect users. According to the human rights advocacy group Article 19, Grindr could show a less precise distance for users, inverse to the population density of the area. For example, the app would show location with up to 100 meters of accuracy in Manhattan, while showing within 1 kilometer of accuracy in Iceland. This would still offer users’ locations, but someone couldn’t exploit them to find a user’s exact position. However, Grindr’s servers would need to be able to determine the area’s population density, which may be technically complicated to implement, said Article 19 security researcher Norman Shamas.
There is an even simpler measure Grindr could take. After security researcher Max Veytsman found in 2014 that Tinder users’ location data could be exploited, the company updated the app’s servers to show users’ locations in increments of a mile (instead of exact distances with up to 15 decimal places of precision), making trilateration much more difficult.
Still, Grindr has not obscured the highly precise location data that allowed S.P. to track himself sitting in his backyard.
That may be because the “[x] feet away” feature is important to some users in the Grindr community. “It makes a lot of people feel safe, because it makes them feel not alone,” said Faden.
"The precision with which users can be currently located is, at least in my view, outright dangerous."
Afsaneh Rigot, the Iran program officer at Article 19, agrees: “Although these apps have risks, they are quite fundamental for these communities to connect.” Still, in a report on how technology is used to entrap LGBT people in the Middle East, Rigot found that 89% of respondents were more interested in seeing the approximate location of other users, like neighborhood or city, rather than precise location.
“In many countries, Grindr serves an important function by allowing men to meet each other in environments where this would otherwise be difficult. But the precision with which users can be currently located is, at least in my view, outright dangerous,” said Queer Europe’s S.P.
According to Shamas, Grindr’s location data issues go beyond a question of security. “It’s a privacy concern. Compromising privacy leads to issues with trust, which leads to someone using a less secure app.” Shamas added that for Grindr, gaining user trust, and consent, is vital: “The more dire issue is people not having a connection to the community they need to survive.”
Here are some ways to make it harder to track your location through Grindr:
– Whatever you do, said Article 19’s Rigot and Shamas, don’t use a VPN. “A lot of research shows that people are using differing methods to obscure their geo-location, including using a VPN, which doesn’t actually work,” said Rigot. Shamas recommends you turn off your device’s location services when you don’t want to be tracked.
– Disable Grindr’s “Show Distance” feature. Go to your profile, then tap the Settings gear (top right). Scroll down to “Show Distance” and tap the slider to disable. This is will prevent “[x] feet away” from appearing on your profile, and prevent people from locating you through trilateration.
However, because you are still sorted in the grid by order of distance, trilateration may be possible. Grindr warns, “an approximate distance may be inferred,” but disabling the feature makes it more difficult.
– If you’re somewhere you’d rather not disclose, temporarily turn off Location Services for Grindr. On iOS, open Settings, scroll down to Privacy, select Location Services, scroll down to Grindr, and select Never. On Android (9.0 and up), go to Settings and in the search bar, type “App permissions.” In the App permissions menu, tap Location and next to Grindr, tap the slider to disable.
With Location Services turned off, you won’t be able to see any profiles in the grid, but you can still view messages.
CORRECTION
Article 19 program officer Afsaneh Rigot's name was misspelled and her title misstated in an earlier version of this post.
