In a new addition to its regular transparency report, Google has published information about the FBI's use of National Security Letters. Notice anything strange about it?
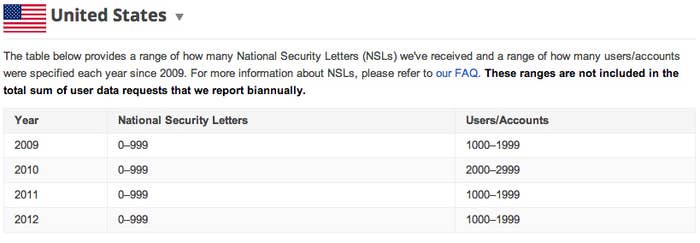
According to Google, the site isn't allowed to disclose exactly how many letters it received, and can only post ranges of affected users. All we really know from these charts is that Google received at least one request a year since 2009, which demanded information about a minimum of a thousand people in every year but 2010, when it was at least 2000.
NSLs allow the FBI to request certain types of user information without going through traditional legal means — they're like instant subpoenas, basically. Google describes them as "request[s] for information that the Federal Bureau of Investigation (FBI) can make when they or other agencies in the Executive Branch of the U.S. government are conducting national security investigations."
So, as a standalone disclosure, Google's chart doesn't tell us much. But the Cato Institute notes that in 2011, the last year data was available, the FBI issued 16,511 NSLs with requests for about U.S. persons, which resulted in 7,201 fulfillments. While Google's data isn't limited limited to U.S. citizens, U.S. citizens traditionally account for the majority of NSL targets. In other words, even if you use Google's lowest offered number, Google accounts for a notable percentage of all NSLs.
But what can the FBI actually get with these letters? NSL's were created in 1978, so the language isn't exactly up to date. Here's what Google says they can be compelled to provide:
"the name, address, length of service, and local and long distance toll billing records" of a subscriber to a wire or electronic communications service. The FBI can't use NSLs to obtain anything else from Google, such as Gmail content, search queries, YouTube videos or user IP addresses.What isn't explicitly addressed is how those outdated words translate — all Google says is what NSL's can't be used for: to hack into your Gmail account or get your IP address from a name.
But apparently, they can be used to connect a name to an already-known IP address. So, say the FBI managed to connect an IP address to some suspicious online activity, but didn't have a name. An NSL sent to Google might be able to connect it to a real identity.
In other words, these things are pretty powerful. And the less we know about them, the worse off we are.
