
A month after 20,000 private emails from the Democratic National Committee were published online, election officials across the country received a series of warnings from the FBI: Hackers were targeting states’ election websites and, in at least one case, were able to steal voter registration data. The Department of Homeland Security has since created an election cybersecurity action campaign, and US intelligence officials have begun investigating the possibility of a covert Russian intelligence operation that seeks to undermine the integrity of the American election.
But despite the growing concerns over foreign meddling coming from Congress, intelligence experts, and the Clinton campaign, state election officials say American voters have little to fear.
“It really saves us from worrying too much about cybersecurity — we have other concerns, but that’s kind of not one of them.”
“There are over 9,000 jurisdictions that operate elections at a very local level, so that’s both a blessing and a curse,” Denise Merrill, Connecticut’s secretary of state and president of the National Association of Secretaries of State (NASS), a nonpartisan organization that represents the country’s top state election officials, told BuzzFeed News. “It really saves us from worrying too much about cybersecurity — we have other concerns, but that’s kind of not one of them.”
Merrill was appointed by NASS to join Homeland Security’s special working group on election cybersecurity. The group's goal is to build closer ties between the federal government and local election officials, and also to consider designating state voting systems as “critical infrastructure,” akin to dams and power grids, granting election offices additional resources and protections from the federal government.
Merrill, along with the secretaries of state and election officials representing California, Florida, Ohio, Minnesota, Colorado, and Iowa, told BuzzFeed News that pre–Election Day simulations, paper trail audits, and the fact that voting machines are not connected to the web provide strong safeguards to the electoral system.
State election officials emphasized that the recent hack into voter registration databases differs from the risks faced by their offices, because these databases aren’t directly tied to voting on Election Day and because voting machines cannot be accessed remotely through the internet. “That’s the voter registration system, which is not at all connected to the actual voting,” Merrill said, adding that in almost every state, voter registration is completed on paper. “There are backup paper systems for every process in our election, and that means cybersecurity is not the concern that it’s being portrayed to be nationally.”
While internet connected computers do face an array of vulnerabilities, there are other ways to introduce sabotage. “The fact that most of these machines aren’t connected to the internet doesn’t make them immune to malicious software," Ariel Feldman, a computer science professor at the University of Chicago, told BuzzFeed News. “In fact, our initial study, many years ago, demonstrated a voting machine virus that spread from machine to machine — not on the internet, but over memory cards,” he said.
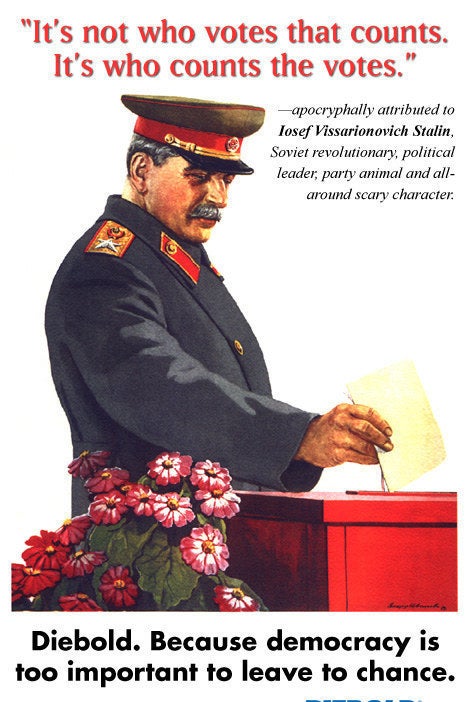
In 2006, Feldman was part of a three-person research team at Princeton University that published an influential study demonstrating startling vulnerabilities in the Diebold AccuVote-TS voting machine, the most widely used voting machine in America at the time (and one viciously parodied in a faux ad campaign called "The Diebold Variations"). “There are various places where malicious software can be injected into the electoral process, and spread very broadly, even beginning with voting machine manufacturers,” he said.

Other experts have pushed back against the argument that our decentralized voting system provides adequate protection against outside interference. “Those 9,000 jurisdictions are still purchasing their election software from the same four or five vendors,” Andrew Appel, a computer science professor at Princeton University, told BuzzFeed News. “So there aren’t 9,000 different kinds of election systems to hack, there’s just a few kinds,” he said. Appel added that some of those jurisdictions might be situated in competitive swing states, where the margins of victory are small and only hundreds or thousands of votes determine the final outcome.
Five states — Georgia, New Jersey, Louisiana, South Carolina, and Delaware — exclusively use machines that generate no paper audit trail.
This November, about 75% of American voters will cast their ballots on paper or on a machine that produces a paper record, according to Pamela Smith, the president of Verified Voting, a nonpartisan watchdog organization focused on electoral accountability. But five states — Georgia, New Jersey, Louisiana, South Carolina, and Delaware — exclusively use machines that generate no paper audit trail. This, experts say, makes it difficult to determine whether those machines accurately capture the preferences of voters. Several other states, including some of the country’s most populous, like Texas, Pennsylvania, and Virginia, use paperless voting machines in at least some of their districts.
Of course, having a paper record does not in itself make voting machines less vulnerable to hackers who gain physical access to them. Nor do paper audit trails prevent software malfunctions. But they can act as a deterrent and fail-safe, according to Lawrence Norden, the deputy director of the democracy program for the Brennan Center for Justice and co-author of a recent study that catalogued the state of US voting machines.
Norden told BuzzFeed News that the national trend is moving away from paperless voting machines. But many of the machines still in use are woefully out of date and are serviced by election offices with meager budgets. However, election officials have come to realize that the idea of Election Day hacking has moved from the theoretical into the real, he said.
“Fortunately this is something that we’ve been talking about for years,” Ohio Secretary of State Jon Husted told BuzzFeed News. Ohio has not seen any attempted hacks into its election-related websites, Husted said. And the IP addresses linked to the Arizona and Illinois breaches, which the FBI shared with election officials, have been flagged by his office and have not been detected.
Ohio, like other states BuzzFeed News spoke with, limits physical access to voting machines, conducts audits before and after Election Day, and has sought help from state and federal law enforcement in detecting cybersecurity threats. “This latest news is just one more moment for us to go back and double-check our work to make sure we have done it the right way,” Husted said.
“You can’t hack a paper ballot. Sometimes old technology is good.”
100% of votes cast in Ohio on Election Day will generate a paper record, Husted said, a practice that several other states pointed to as a robust preventive measure against manipulation. “You can’t hack a paper ballot. Sometimes old technology is good.”
“Ironically, in this high-tech age, good old-fashioned paper provides a lot of security,” Minnesota Secretary of State Steve Simon told BuzzFeed News. “Unlike other states that have in the last 15 years adopted systems that are completely or mostly electronic, we vote in Minnesota on paper ballots.” In addition to a state-mandated paper audit trail, Simon said, Minnesota has brought in private-sector firms to conduct an outside audit of election systems’ security.
But even the most thoughtful defensive measures can be circumvented by determined and creative adversaries, a fact acknowledged by California Secretary of State Alex Padilla, who said that his state is constantly testing its voting equipment and seeking expertise from federal law enforcement to stay ahead.
And beyond compromising specific vote tallies, other officials have said that merely casting doubt on the electoral results may diminish public confidence in the democratic process. “For me the worst thing about all this is that it’s creating suspicion in the American public that really could be destructive,” said Secretary Merrill of Connecticut.
The Department of Homeland Security has continued to offer its assistance to election officials in the form of security audits, incident response plans, and information sharing, according to the agency’s chief, Jeh Johnson. But even as the feds are eager to help, Johnson characterized the idea of an Election Day hack as a far-fetched scenario. “It would be very difficult, through any sort of cyber intrusion, to alter the ballot count, simply because it is so decentralized and so vast,” Johnson said Thursday during an event hosted by The Atlantic.
Some state election officials have expressed concerns that the fears aroused by vote manipulation may invite a heavy-handed response from the federal government, encroaching on the authority of state and local election offices, according to several secretaries of state who were on a conference call with Johnson last month. But Johnson said Homeland Security is merely offering help to those who ask. “There’s a lot of chatter on the internet about what that could mean — it does not mean a federal takeover of state elections systems,” he said. "We don’t have the authority to do that. What we do in Homeland Security, in cybersecurity, is offer some assistance when people ask for it.”
