
Twitter continues to approve malicious ads that, in at least one case, masqueraded as an offer from Twitter itself to help users get their accounts verified.
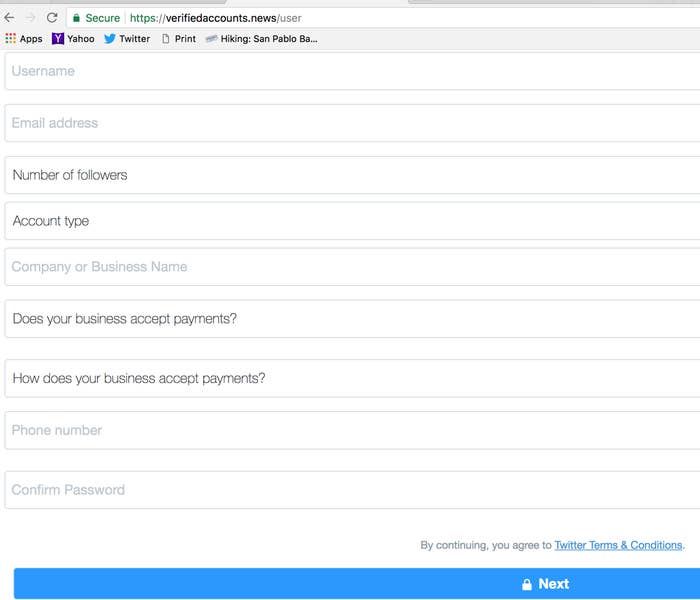
The ads led users to a website that asked for account information such as their email address and Twitter password, in addition to requesting details about the user's online payment accounts.
"These are nothing less than phishing attempts designed to steal users’ credentials as well as their financial information," Jérôme Segura, the lead malware intelligence analyst for Malwarebytes, told BuzzFeed News. "The harvested data is typically resold in bulk on various darkweb marketplaces."
When combined with the email address and other information collected in the form, the payment details could be used to break into a user's online payment accounts.
Segura said this type of phishing attack has been running on Twitter "for years," and frequently exploits the platform's Promoted Tweets advertising product. A similar scheme was identified early last year. Twitter's Promoted Tweets product enables a user to take a tweet from their account and turn it into an ad that can appear in other people's timelines.
This attack could be also used to target specific users in order to gain access to their Twitter account, as well as related online accounts, according to Segura.
"Because promoted tweets can be configured to be displayed for a particular audience, they could in theory be used for more targeted phishing campaigns as well," Segura said.
Twitter's advertising policies are already under scrutiny after it acknowledged late last year that Russian government broadcaster RT spent $1.9 million on the platform since 2011. Twitter announced in October that it would no longer accept advertising from RT or Sputnik.
"We don't comment on individual accounts for privacy and security reasons," a Twitter spokesperson told BuzzFeed News.
The company's online FAQ about the ad approval process says that ads "are submitted for approval on an automatic basis, based on an account’s advertising status, its historical use of Twitter, and other evolving factors."
At least two different Twitter accounts were able to buy promoted tweets that told users they could get their accounts verified by visiting Verifiedreview.today. That site displayed a form made to look like it was hosted on the official Twitter website. Users were asked for their name, email address, Twitter username, password, and company names, as well as to indicate whether they use any online payment services. Once submitted, the hackers on the other end would be able to login to the person's Twitter account and take it over, or to sell the information.
Verifiedreview.today is no longer online, and the two accounts that shared the link in promoted Tweets have been removed from Twitter. One of them was designed to look like an account run by Twitter itself:

Another account that spread the link via a different ad looked more like a regular user:
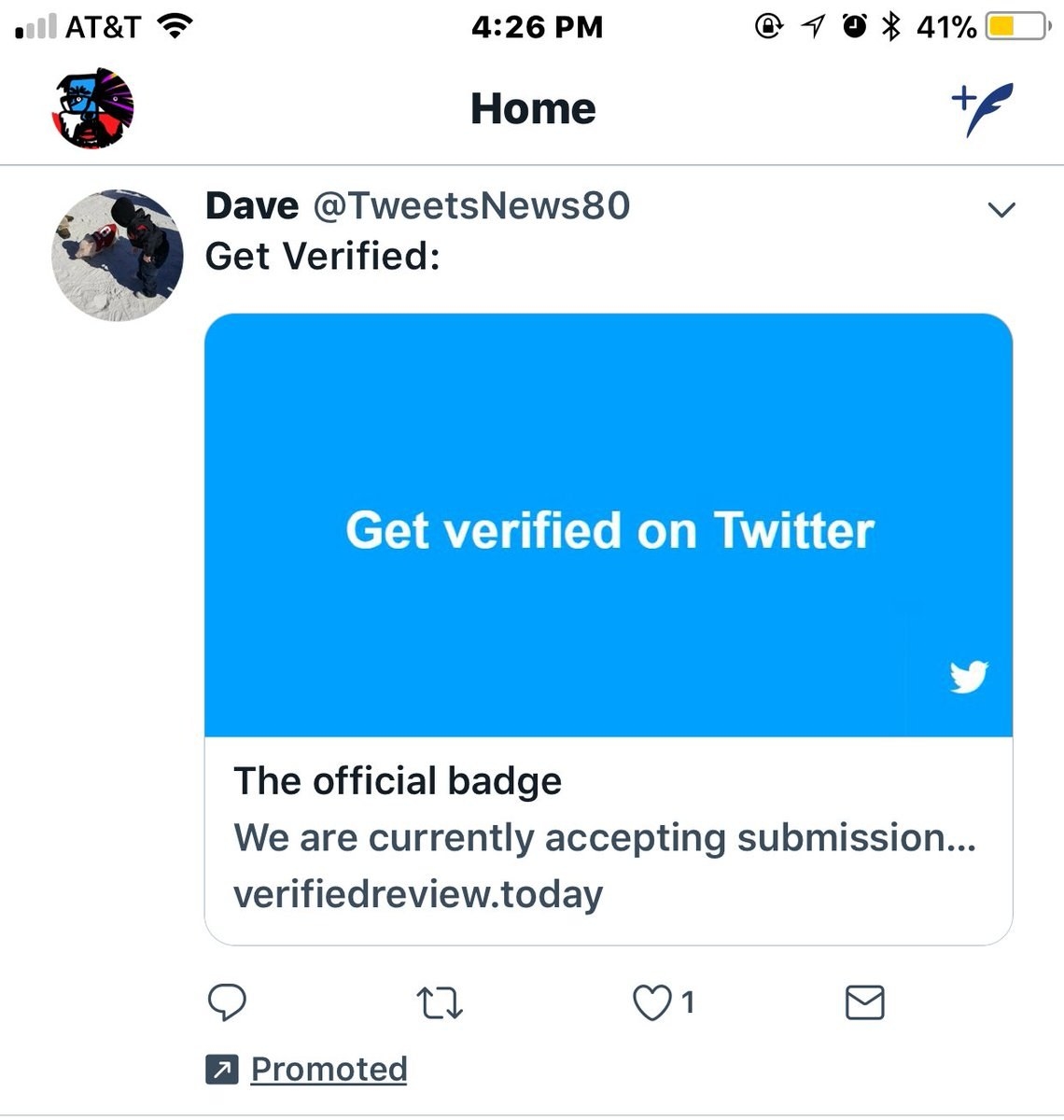
The first ad ran on Jan. 5, and the second appeared two days later, showing that the attack was executed over multiple days using at least two different accounts. In both cases Twitter did not block the ads.
Some said the ability of hackers to run these ads reveals flaws in Twitter's ad approval system.
This is a great example showing how these ad platforms (Twitter, Facebook, Google) know nothing about the entities… https://t.co/5zw6tSuVs1
Nancy Levine, an author based in California, told BuzzFeed News she saw one of the malicious ads in her timeline and clicked through because she thought it came from Twitter.
"I filled out their form, and started typing my password when I became suspicious,' she said in an email. "Looked more closely, then reported it to Twitter as 'spam' — [the] closest available complaint among their menu choices."
Levine said Twitter's opaque rules for verifying user accounts create an opportunity for these scammers.
"As for Twitter verification, I've had four books published by Penguin Books, bylines include Sports Illustrated, AlterNet, and others, but Twitter has declined my application for verification twice," she said. "The scammers played on Twitter users' frustration around verification IMHO."
