It was a weed that Google kept trying and failing to kill.
The browser extension MyPDF kept appearing and being removed from the Chrome Web Store. Its most recent stint saw it gain more than 20,000 installs before Google booted it as a follow-up to the company’s recent removal of more than 500 malicious extensions.
"We take policy violations seriously. If we find any extension on the Chrome Web Store that violates our policies, we take action,” a Google spokesperson told BuzzFeed News.
The mass removal was Google’s largest action against extensions that security researchers said committed ad fraud. The extensions promised useful tasks like converting webpages into PDFs. But once installed, they injected ads and generated massive amounts of invalid traffic, the ad industry’s term for fake or manipulated views, users, or clicks.

Neither Google nor researchers at Duo, the security company that flagged the extensions to the tech giant, revealed who was behind the scheme. But a BuzzFeed News investigation, conducted with cybersecurity firm White Ops and traffic authentication company DoubleVerify, found more than 60 extensions exhibiting the malicious behavior were owned by Daniel Yomtobian, the founder and CEO of Advertise.com Inc., a company that sells web traffic and digital ad products.
A Google spokesperson told BuzzFeed News that Yomtobian’s apps operated as part of the same malvertising campaign.
Yomtobian is a gregarious Los Angeles entrepreneur who for roughly 20 years has run companies that infected personal computers with adware and earned money from what White Ops and DoubleVerify identified as fraudulent web traffic.
In early March, Yomtobian acknowledged owning a browser extensions business, which he told BuzzFeed News he began shutting down “about a month ago.” He said the ad injections performed by his extensions were disclosed to users and in line with Google's policy; he denied being responsible for fraudulent or invalid traffic.
“To be clear, I and Advertise.com have never operated an ‘ad fraud traffic scheme,’” Yomtobian said in an email response to BuzzFeed News. “We have never generated ‘fraudulent traffic.’”
Roy Rosenfeld, the head of DoubleVerify’s fraud lab, told BuzzFeed News that at their peak, Yomtobian’s extensions generated “at least tens of millions of visits a day to different sites,” resulting in hundreds of millions of ad impressions — the total number of times a digital ad displays on a screen. Rosenfeld said traffic it deemed invalid at times ended up on major websites, including Elle.com. A spokesperson for Hearst Magazines, the publisher of Elle, said the company “has no commercial relationship with Advertise.com.”
“We are looking into this and will continue to monitor as we do all traffic sources,” the spokesperson said.
Yomtobian declined to comment on White Ops’ and DoubleVerify’s reports that his extensions generated invalid traffic. He said Advertise.com and its customers used “3rd party traffic verification tools and were satisfied with the traffic.”
Yomtobian’s story is a case study in how digital advertising has become a playground for canny operators who amass fortunes by siphoning money out of the digital ad ecosystem. Brands spent more than $300 billion buying digital ads globally last year, and one estimate said roughly $40 billion of it was stolen due to ad fraud. Seemingly legitimate companies and executives are involved in, or benefiting from, invalid traffic and other forms of ad fraud at massive scale.
Ad fraud researchers, advertising companies, and ad tech professionals have known about Yomtobian for years. News articles called out his alleged schemes as early as 2003, and he has been sued for allegedly helping force malicious software onto PCs. (That suit was settled.) But in spite of his reputation within the industry, he’s never been publicly connected to a high-profile takedown related to ad fraud — until now.
Yomtobian’s shadow stretches beyond his web extensions operation. Advertise.com has provided traffic to the websites of major publishers, such as Bonnier, which owns Popular Science; Edmunds, an automotive publisher; and Gannett, the owner of USA Today and 260 local newspapers.
“We no longer work with Advertise,” said a Bonnier spokesperson, who declined to comment further.
Two Bonnier sites — CycleVolta.com and UTVDriver.com — received traffic from Yomtobian extensions last year, according to DoubleVerify. A source with knowledge of Bonnier’s operations said the publisher cut ties with Advertise.com last summer after it commissioned White Ops and another detection firm, IAS, to review its traffic providers. The resulting report identified invalid traffic and other concerns, the source said.
An Edmunds spokesperson declined to comment on its sources of traffic and the companies with which it works.
“We don’t work with Advertise.com at this time,” said a Gannett spokesperson.
"Daniel is one of the nicest guys you’ll ever want to meet,” a former customer, who asked not to be named for fear of retaliation, told BuzzFeed News, “but a lot of con men seem like great guys until you understand what they really are.”
Yomtobian’s main business is selling web traffic, and it’s made him fabulously rich.
When his sister, a forensic psychologist and adjunct professor of psychology at the University of Southern California, was married in 2016 at his home, the New York Times covered it in its Vows column. It described Yomtobian’s $14 million Beverly Hills estate as a “15,000-square-foot mansion with palatial floor-to-ceiling windows in the living room and a flowing terrace that offered breathtaking views stretching from Los Angeles to the Santa Monica skyline.”
Yomtobian was a regional finalist for the Ernst & Young Entrepreneur of the Year award, a regular exhibitor at advertising trade shows, and claims to have won “a Mashable Award and a CNET Webware 100 Award.” (He was actually the runner-up for the Mashable award.) The media even has quoted Yomtobian as an expert in ad fraud prevention.
Advertise.com, which Yomtobian founded in 2001 as ABCSearch.com, bills itself as “the world's largest privately held keyword pay-per-click (PPC) network” and reportedly had $35 million in revenue in 2012, the only time Yomtobian appears to have publicly disclosed financial information.
Advertise.com says it can deliver millions of visitors and clicks thanks to traffic that “can’t be acquired anywhere else.” It claims to have served more than 10,000 clients since 2001. It’s one of many such businesses that trade in web traffic, a significant and shady sector of the online advertising and publishing industry.
A publisher might buy traffic to hit goals it promised to an advertiser or to increase ad views and therefore revenue. Yomtobian at times generates traffic in ways that force people — or their browsers, at least — to visit websites they had no intention of viewing, while disguising the origin of these visitors to trick analytics software and fraud detection services.
In one example of Yomtobian Chrome extension behavior documented by DoubleVerify, a user clicked a link on a website in their browser. But instead of loading the correct page, a new browser tab automatically opened and loaded Elle.com. This registered as a visit to Elle.com, from which the site's owners could earn money from ads on the page.
Friedman, the Hearst spokesperson, said it doesn’t work with Advertise.com and that it provides “advertising services that exceed industry standards in ad verification, fraud prevention, brand safety and viewability.”
DoubleVerify found Yomtobian’s extensions attempted to disguise the origin of this invalid traffic. One method was adding false referral information in URLs to make the traffic appear to have originated on Taboola or other ad networks, rather than the browser extension. Some of this spoofed Taboola traffic was sent to Bonnier sites CycleVolta.com and UTVDriver.com, according to DoubleVerify.
The source with knowledge of Bonnier said the Taboola spoofing was not previously known to the company.
A former Advertise.com employee told BuzzFeed News they were told to mislead customers about where traffic originated.
“There was lying going on. We were instructed at some points to lie to our partners about where the traffic was coming from and what kind of traffic it was,” said the ex-employee, who asked not to be named so they could speak freely about the business's internal operations.
“Dan’s goal is just to constantly make as much money as he can, and it didn’t matter if it was going to compromise any publisher or any advertiser’s integrity or business model,” they said. “I think he’s really oblivious as to the degree of how wrong it is. I don’t know how he could do it with a conscience.”
“I have never instructed anyone to lie about the origins of traffic being sold,” Yomtobian responded. “We have always been completely transparent with our advertisers about the type of traffic, implementation, and user experience.”
It was 2003, and people around the world were angry.
A piece of software called Xupiter had infected their web browsers. The browser toolbar changed their homepages to Xupiter.com, routed internet searches through that site, downloaded other applications, launched annoying pop-up windows, and redirected users to sites they had never typed into the address bar.
Wired labeled it “the most evil thing on the Internet,” BBC News deemed it a “web hijacker,” and the forums on SpywareInfo reportedly had more than 25,000 posts about the software and how to remove it.
In 2002, Yomtobian, who grew up in the Los Angeles area and started buying domains and building websites while in college, registered Xupiter Inc. in California. Soon, scores of websites owned by Yomtobian or his father, Saeid, advertised the toolbar for download. Wired pointed the finger at them, as did the Wall Street Journal and a report published on WebDefenders.net. Wired said the father and son were “experienced in devising innovative ways to use the Internet to force their businesses down people's throats.”
Yomtobian declined to comment on Xupiter. But after webdefenders.net published the report, he sent a cease-and-desist letter, claiming the article contained false and defamatory statements. Christopher Carlino, a coauthor of the Xupiter report, said they removed it from the site because they lacked the legal resources to fight. However, Ben Edelman, a former Harvard professor and expert in digital advertising, published a summary in 2006, calling it “impressive, detailed, useful work — properly citing its sources to persuade me of its accuracy.” (Edelman now works for Microsoft and was not able to speak publicly about Xupiter.)
Xupiter eventually faded as people figured out how to remove it. But Yomtobian did not.
Later that year, the Wall Street Journal reported that Yomtobian’s search site, ABCSearch.com, had placed ads from major brands like Home Depot next to links to hardcore porn sites. (In 2009, ABCSearch.com rebranded as Advertise.com.)
Around the same time, Daniel Yomtobian was involved in an online business called Sexual Cash, and he later owned domains BackdoorDudes.com, DildoLesbos.com, and TeeniCummers.com, according to registration records from DomainTools. Wired reported that the Yomtobians were “well-known spammers who have been accused of hijacking other peoples' mail servers to pump out solicitations for porn sites.”
Daniel declined to comment on Sexual Cash but denied he was a spammer. “I have never been involved in email spam, period. Nor have I ever had any involvement in hijacking anyone’s email server,” he said.
The WSJ story also reported that Saeid Yomtobian owned more than 78,000 domains. He was sued by publishers, including the Los Angeles Times, which alleged that some of those domains, such as LATime.com, infringed on its trademarks. In one case, Fairchild Publications alleged that Saeid used a domain with a name similar to Children’s Business magazine, which it owned, “to direct computer users to an ‘extreme’ porn site called SexHorse.com.” A World Intellectual Property Organization arbitration panel agreed and ordered the domain transferred to Fairchild.
Saeid, who did not respond to an emailed request for comment, later changed his name to Luigi “Kari” Bian and is now a low-budget film producer whose releases have featured actors Vivica A. Fox, Jon Lovitz, and Cheech Marin.
In 2015, Bloomberg published an investigation into digital ad fraud. One section of the story examined low-quality web traffic flowing to websites operated by Swedish publishing giant Bonnier, including Saveur.tv and WorkingMotherTV.com.
In the span of six months, the sites went from zero visitors to millions per month. A Bonnier executive said it bought traffic “to prime the pump” and see if it could earn more money from ads than it paid for the audience. One ad firm, SiteScout, blocked the sites for what it deemed “excessive nonhuman traffic,” according to Bloomberg. But Bonnier said it paid for human users and used reputable fraud detection firms to measure the traffic.
Bloomberg tracked the traffic back — and landed at Daniel Yomtobian’s door.
“I’ve found Advertise.com selling every type of worthless traffic I am able to detect,” Edelman, the former Harvard Business School professor, told Bloomberg. “And doing so persistently, for months and indeed, years.”
Yomtobian argued his traffic was legitimate. “There is a huge distinction between worthless traffic and low-quality traffic,” he said.
By 2017, Yomtobian was supplying traffic to sports sites owned by newspaper giant Gannett, including MMAJunkie.com and TheBigLead.com. Each site operated a subdomain — video.MMAJunkie.com, for example — that received Advertise.com traffic and earned money from video ads.
That same year, BuzzFeed News exposed an ad fraud scheme involving websites secretly operated by an advertising industry insider, as well as a group of sites run by Katarina Van Derham, a model who once appeared on HBO’s Entourage as actor Bob Saget’s girlfriend.
When asked how a food site that was never updated with new content managed to generate such a big audience, Van Derham attributed it to “a marketing campaign on advertise.com.”
Yomtobian was also directing dubious traffic to his own sites in 2017. Another company he owned, Web Value Inc., operated news and culture websites with names such as LosAngelesPost.com, VitalWorldNews.com, and BuzzIntersection.com, among others. BuzzFeed News documented how these sites received traffic originating on porn sites like YouPorn.com.
Anytime a user clicked a link on the porn site, it opened a small pop-under browser window behind the main window. The pop-under window generated by Advertise.com was programmed to remain hidden for a set amount of time, when it would expand, redirect through different domains, and load a video subdomain on one of Yomtobian’s sites.
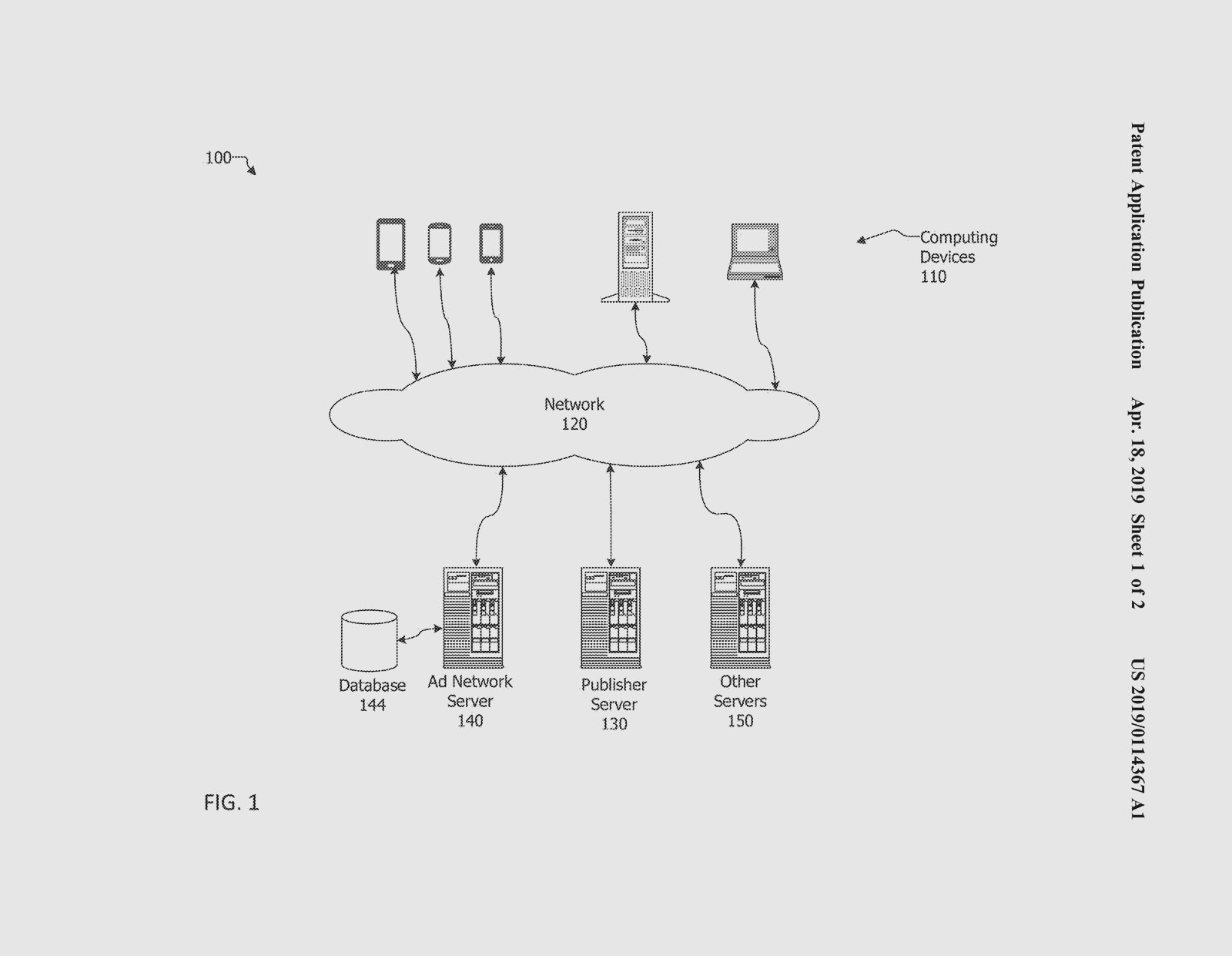
Yomtobian defended the practice, saying he had a patent on the use of hidden browser windows that expand, and denying it was ad fraud. “Major websites, including travel sites, currently employ similar technology,” he said. The patent description notes that by using “this method, the consumer will be unaware of the publisher that caused the ad window and related ad to appear.”
The former Advertise.com employee said Yomtobian at one point spent $300,000 a month to buy traffic for his own domains, and that it was a profitable operation. “Where Dan was really getting the bulk of his money was on his side projects,” they said.
In some cases, he was making that money using stolen content. Prior to being taken offline recently, LosAngelesPost.com was filled with plagiarized articles from Lifehacker and other sources.
Another Web Value Inc. site, OurNewsToday.com, recently consisted almost entirely of articles plagiarized from CBS News. (An archived version of a 2017 article on the site was also copied word for word from CBC.ca.) Data from SimilarWeb shows OurNewsToday.com received a significant percentage of its audience from Advertise.com traffic, some of which originated from Yomtobian’s browser extensions.
Yomtobian took OurNewsToday.com offline after being asked about the plagiarized content and did not respond to questions about the site.
Another recipient of manipulated traffic originating from Advertise.com was Edmunds.com, the popular auto website. Last year, a major referrer to the site was SaabDealers.com, according to data from SimilarWeb. That site, which has no connection to the automaker, received traffic from pop-under windows and tabs sold by Advertise.com. Some of this traffic originated from pop-unders on porn and illegal streaming websites, according to data from SimilarWeb.
SaabDealers.com redirected those visits to Edmunds.com. This traffic laundering made it appear in web analytics reports that users visited SaabDealers.com and followed links to Edmunds.com, which they had not.
Yomtobian declined to comment on Edmunds.com traffic, but denied involvement in domain redirect or traffic laundering schemes. “I'd like you to know that the advertisers chose what url or redirect to use once the traffic was delivered to them. We did not control that,” he said.
An Edmunds spokesperson declined to comment on any relationship with Advertise.com and the traffic it purchases.
“Edmunds generates traffic from a number of sources, but it's not our policy to share specifics or details surrounding our work with third parties,” said Talia James-Armand, Edmunds’ senior manager of public relations.
As recently as last year, Yomtobian was still providing traffic to some of Bonnier’s sites. He also hosted and provided translation services for a Spanish-language version of the Popular Science website, though the contract forbade Yomtobian from sending traffic to it, according to Bonnier.
In midsummer 2019, Bonnier cut all ties with Yomtobian after it hired White Ops and IAS to look more closely at its traffic partners. A source with knowledge of the report said it identified invalid traffic and other issues.
A spokesperson for Gannett declined to comment other than to say it no longer works with Advertise.com.

By the fall, Yomtobian became aware that BuzzFeed News was looking into his web of businesses.
“I heard through the grapevine that you are looking for information about Advertise.com,” he said in an email. “In reviewing your bio I can see that you have an interest in online advertising and more specifically in popunder ad units.”
Yomtobian said that he would no longer sell pop-under ads.
“While popunders are legitimate ad units and are not deemed invalid by [the Media Ratings Council], Advertise.com recognizes industry trends and has decided to eliminate popunder ad units from its suite of offerings,” he said. “Just to be clear, popunders are no longer available from Advertise.com.”
By the time he sent that email in late October, there had been a notable decline in traffic from Yomtobian’s network of browser extensions, according to DoubleVerify’s Rosenfeld.
“They started to wind down a few weeks before that, and by that time they were mostly gone,” he said.
But it seems Yomtobian couldn’t stay away. By January, Rosenfeld said his team was tracking the same type of invalid traffic coming from “new extensions that were added recently and also re-uploaded extensions that were removed from the store in the past.”
By February, Google removed many of Yomtobian’s extensions as part of the larger sweep of more than 500 extensions engaged in malvertising.
With his extensions banned by Google and flagged for invalid traffic by DoubleVerify and White Ops, and longtime partner Bonnier walking away due to similar concerns, it might seem like Yomtobian’s run is coming to an end. But a former client predicted he'll be back.
"He changes businesses and business models based on whatever is the hottest thing at the time." ●
CORRECTION
Jon Lovitz’s name was misstated in an earlier version of this post.